What Is the Potential Impact of Quantum Computing on Data Security?
In the ever-evolving field of technology, quantum computing has emerged as a game-changer. With its ability to solve complex problems at an exponential speed, it holds immense promise for various industries. However, as with any new technology, there are concerns about its potential impact on data security. In this article, we will explore the potential implications of quantum computing on data security and discuss the challenges that need to be addressed.
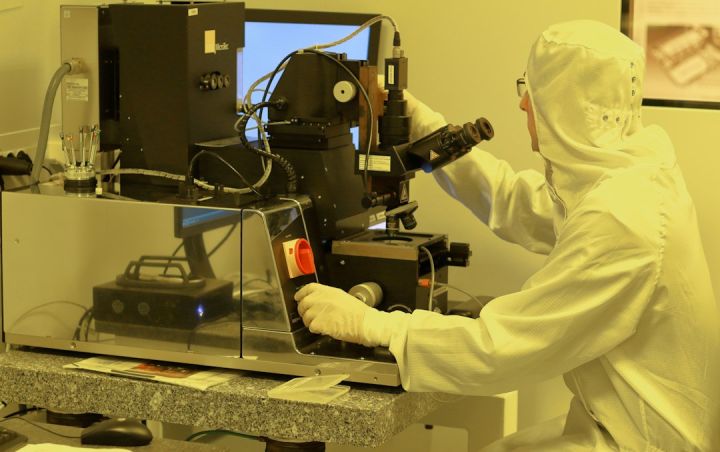
Understanding Quantum Computing
Before delving into the potential impact on data security, it is essential to grasp the basics of quantum computing. Unlike classical computers that use bits to store and process information, quantum computers use quantum bits, also known as qubits. These qubits can exist in multiple states simultaneously, thanks to a concept called superposition. This unique property allows quantum computers to perform parallel computations, making them exponentially more powerful than classical computers.
Potential Threat to Encryption
One of the most significant concerns surrounding quantum computing is its potential threat to encryption. Encryption is a fundamental aspect of data security, ensuring that sensitive information remains secure and inaccessible to unauthorized individuals. Currently, most encryption algorithms rely on the difficulty of factoring large numbers, a task that is extremely time-consuming for classical computers. However, quantum computers have the potential to crack these algorithms with ease due to their ability to quickly factor large numbers using algorithms such as Shor’s algorithm.
Post-Quantum Cryptography
To mitigate the threat posed by quantum computers, researchers are actively working on developing post-quantum cryptography. This form of cryptography aims to create algorithms that are resistant to attacks from both classical and quantum computers. By transitioning to post-quantum cryptographic algorithms, organizations can ensure the long-term security of their data even in the presence of quantum computers. However, implementing and transitioning to these new algorithms poses its own set of challenges, including compatibility issues and the need for widespread adoption.
Quantum Key Distribution
Another potential solution to the threat posed by quantum computers is quantum key distribution (QKD). QKD utilizes the principles of quantum mechanics to securely distribute encryption keys. Unlike classical key distribution methods, QKD provides unconditional security, as any attempt to intercept or measure the quantum key would disturb it, alerting the sender and recipient. This ensures that the keys used for encryption remain secure, even in the presence of quantum computers. However, QKD is still in its early stages of development and faces challenges such as limited range and the need for specialized infrastructure.
Securing Data in the Quantum Era
As quantum computing continues to advance, it is crucial for organizations to start preparing for the quantum era. One approach is to develop quantum-resistant encryption algorithms that can withstand attacks from quantum computers. Additionally, organizations should invest in research and development to explore new cryptographic techniques that can provide enhanced security in the quantum era. Furthermore, establishing international standards and regulations for data security in the quantum era is essential to ensure a global approach to protecting sensitive information.
Conclusion: Safeguarding the Future
While quantum computing holds immense potential for solving complex problems, its impact on data security cannot be ignored. The ability of quantum computers to crack encryption algorithms poses a significant threat to the confidentiality and integrity of sensitive information. However, by embracing post-quantum cryptography and developing secure key distribution methods, organizations can safeguard their data against attacks from quantum computers. It is imperative for researchers, policymakers, and organizations to work together to address the challenges posed by quantum computing and ensure a secure future in the quantum era.